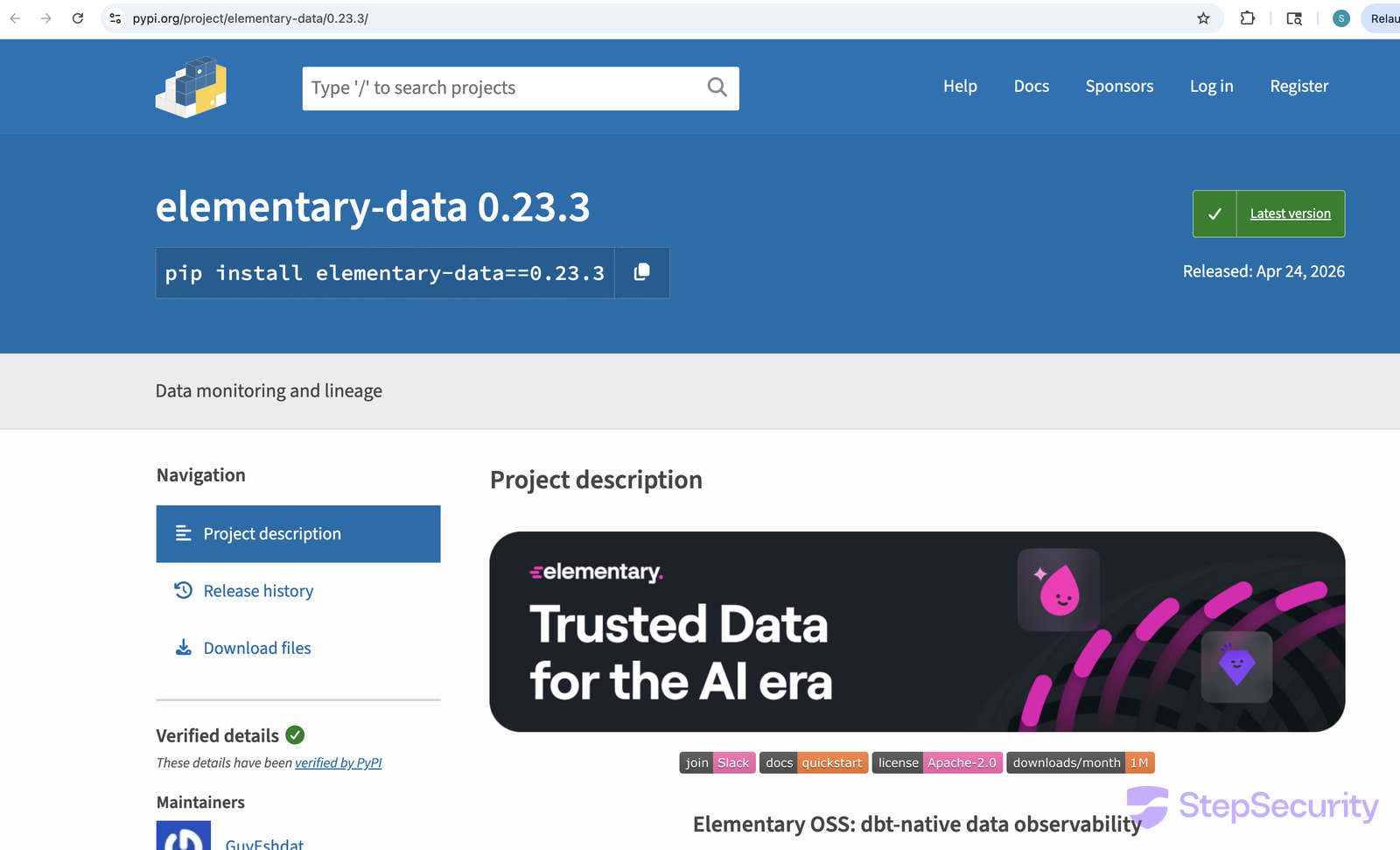
An Attacker pushed a Malicious version of the popular elementary-data package to the Python Package Index (PyPI), aiming to steal sensitive developer data and cryptocurrency wallets.
Next, the dangerous release 0.23.3 extended to the Docker image, because the package’s workflow creates the image from the code and uploads it to a container registry for deployment.
Then, community member crisperik spotted the Malicious upload and opened an issue on the project’s GitHub on Saturday, alerting the maintainer and decreasing the exposure window.
After that, a clean replacement, elementary-data 0.23.4, reached users. However, users who downloaded the malicious variant remained compromised.
Meanwhile, the elementary-data package serves as an open-source data observability tool for dbt, primarily used by data/analytics engineers working with data pipelines. Notably, it remains a popular tool in the dbt (Data Build Tool) ecosystem, with more than 1.1 million monthly downloads on PyPI.
Attack Vector: GitHub Actions Exploit
According to an analysis of the incident published by StepSecurity researchers, the Attacker Exploited a flaw in the project’s workflow, rather than compromising the maintainers’ accounts, as is more common with rogue updates.
Specifically, the attacker posted a Malicious comment on a pull request that exploited a GitHub Actions script Injection flaw, causing the workflow to execute attacker-controlled shell code.
As a result, this action exposed the Workflow’s GITHUB_TOKEN, which the attacker then used to forge a signed commit and tag (v0.23.3) and trigger the project’s legitimate release pipeline.
Subsequently, the pipeline built and published the Backdoored package to PyPI as well as a Malicious image to GitHub Container Registry, making it appear as an official release.
The malicious release on PyPI
Source: StepSecurity
Malicious Payload and Data Theft Capabilities
The Malicious release contained the file elementary.pth, which executed automatically at startup to load a secrets stealer targeting the following types of data:
- SSH keys, Git credentials, cloud creds (AWS/GCP/Azure)
- Kubernetes, Docker, and CI secrets
- .env files and developer tokens
- Crypto wallet files (Bitcoin, Litecoin, Dogecoin, Zcash, Dash, Monero, Ripple)
- System data (/etc/passwd, logs, shell history)
Furthermore, the researchers state that the same payload reached the project’s Docker image, because the “Release package workflow that uploads to PyPI also has a build-and-push-docker-image job.”
According to StepSecurity, systems that did not use pinned versions pulled the Backdoored build automatically.
For those who Downloaded the Malicious release, Elementary-data==0.23.3, and the images with the tags ghcr.io/elementary-data/elementary:0.23.3 and :latest, should rotate all secrets and restore their environments from a known safe point.
Source: BleepingComputer, Bill Toulas
Read more at Impreza News