A newly disclosed cPanel flaw tracked as CVE-2026-41940 is now actively exploited at scale, allowing attackers to breach websites and encrypt data in “Sorry” ransomware attacks.
This week, developers released an emergency update for WHM and cPanel to fix a critical authentication bypass flaw that allows attackers to access control panels.
WHM and cPanel function as Linux-based web hosting control panels for server and website management. While WHM provides server-level control, cPanel delivers administrator access to the website backend, webmail, and databases.
Soon after its release, researchers reported that attackers actively exploited the flaw in the wild as a zero-day, with exploitation attempts dating back to late February.
Meanwhile, internet security watchdog Shadowserver now reports that attackers have compromised at least 44,000 IP addresses running cPanel in ongoing attacks.
Ransomware Deployment and Impact
Numerous sources told BleepingComputer that hackers have exploited the cPanel flaw since Thursday to breach servers and deploy a Go-based Linux encryptor for the “Sorry” ransomware [VirusTotal].
Additionally, multiple reports confirm that the attacks have impacted websites. On the BleepingComputer forums, for example, a victim shared samples of encrypted files along with the contents of the ransom note.
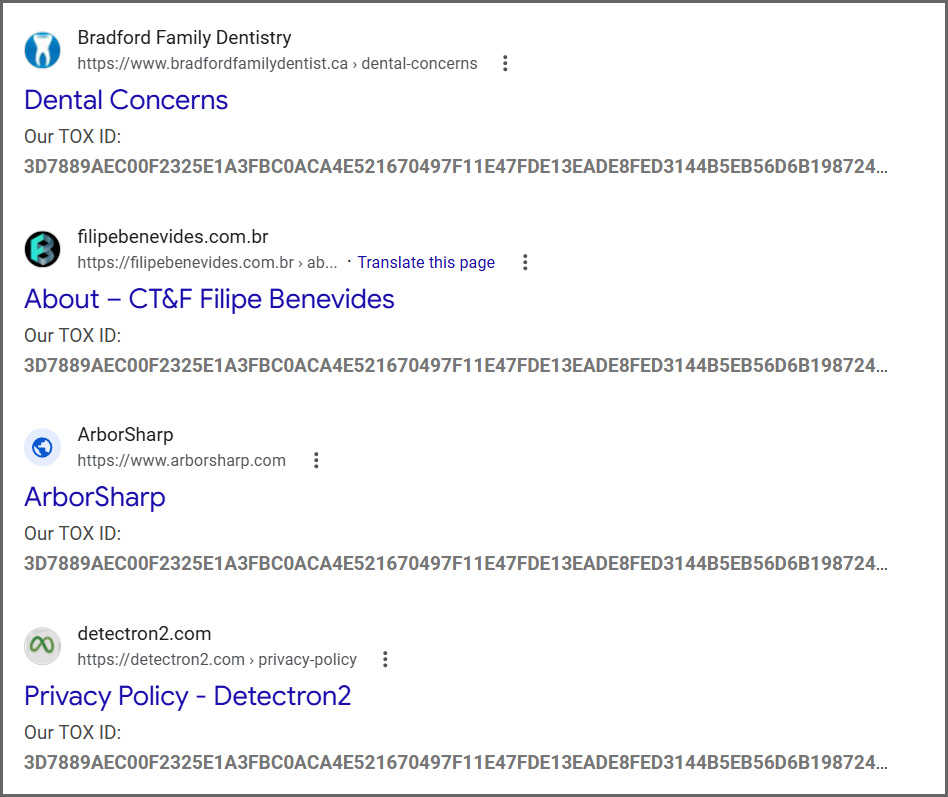
Since then, researchers have spotted widespread exploitation and ransomware activity, while Google has already indexed hundreds of compromised sites.
Google listing of websites hit in Sorry ransomware attacks
Source: BleepingComputer
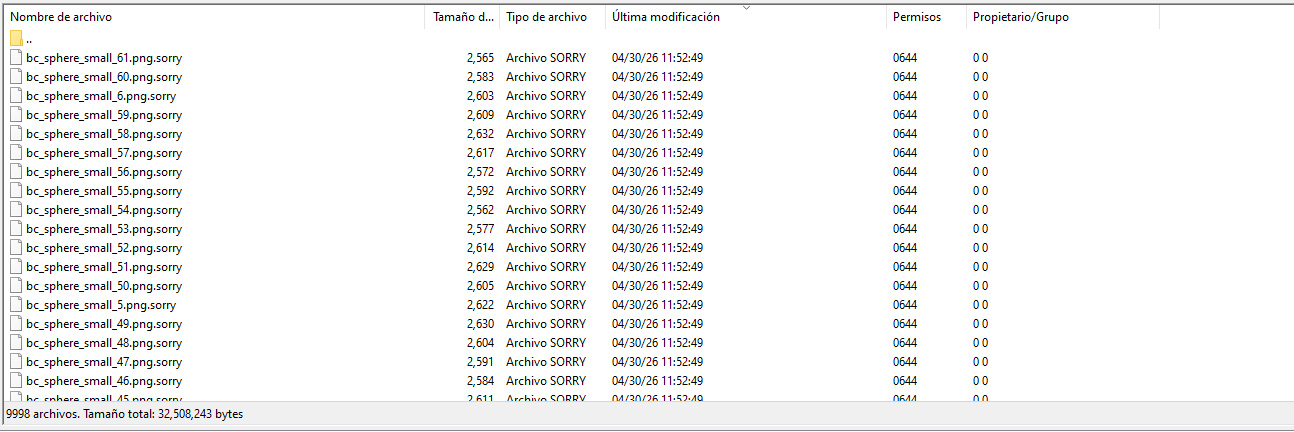
The Sorry ransomware encryptor specifically targets Linux systems and appends the “.sorry” extension to all encrypted files.
Files encrypted by the Sorry ransomware
Source: diozada on the BleepingComputer forums
BleepingComputer confirmed that the ransomware uses the ChaCha20 stream cipher to encrypt files, while it protects the encryption key using an embedded RSA-2048 public key.
Ransomware expert Rivitna explains that the only way to decrypt these files is to obtain the corresponding private RSA-2048 key.
“Decryption is impossible without an RSA-2048 private key,” Rivitna posted to our forums.
Ransom Note and Attacker Communication
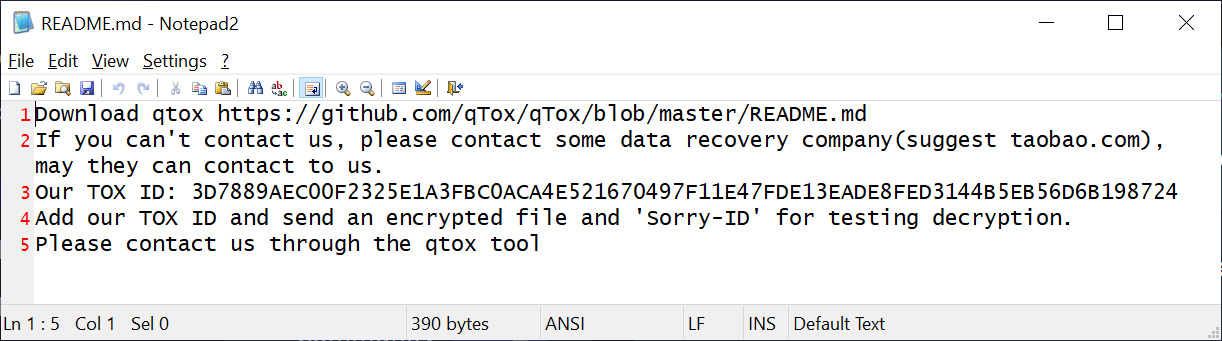
In each folder, the malware creates a ransom note named README.md, instructing the victim to contact the threat actor on Tox to negotiate a ransom payment.
Notably, the ransom note remains identical for every victim in this campaign, including the Tox ID: “3D7889AEC00F2325E1A3FBC0ACA4E521670497F11E47FDE13EADE8FED3144B5EB56D6B198724,” which attackers use for communication.
Sorry ransomware ransom note
Source: BleepingComputer
It is worth noting that a 2018 ransomware campaign used a HiddenTear encryptor to append the .sorry extension. However, this current campaign uses a different encryptor and remains unrelated.
All cPanel and WHM users should immediately install the available security updates to protect their websites from ransomware attacks and data theft.
The attacks have just begun, and security experts expect increased exploitation over the coming days and weeks.
Source: BleepingComputer, Lawrence Abrams
Read more at Impreza News