A new Kyber ransomware operation is actively targeting Windows systems and VMware ESXi endpoints in recent attacks. Notably, one variant implements Kyber1024 post-quantum encryption, signaling a shift toward more advanced cryptographic techniques.
Moreover, cybersecurity firm Rapid7 retrieved and analyzed two distinct Kyber variants in March 2026 during an incident response. Both variants operated on the same network, with one targeting VMware ESXi and the other focusing on Windows file servers.
“The ESXi variant is specifically built for VMware environments, with capabilities for datastore encryption, optional virtual machine termination, and defacement of management interfaces,” explains Rapid7.
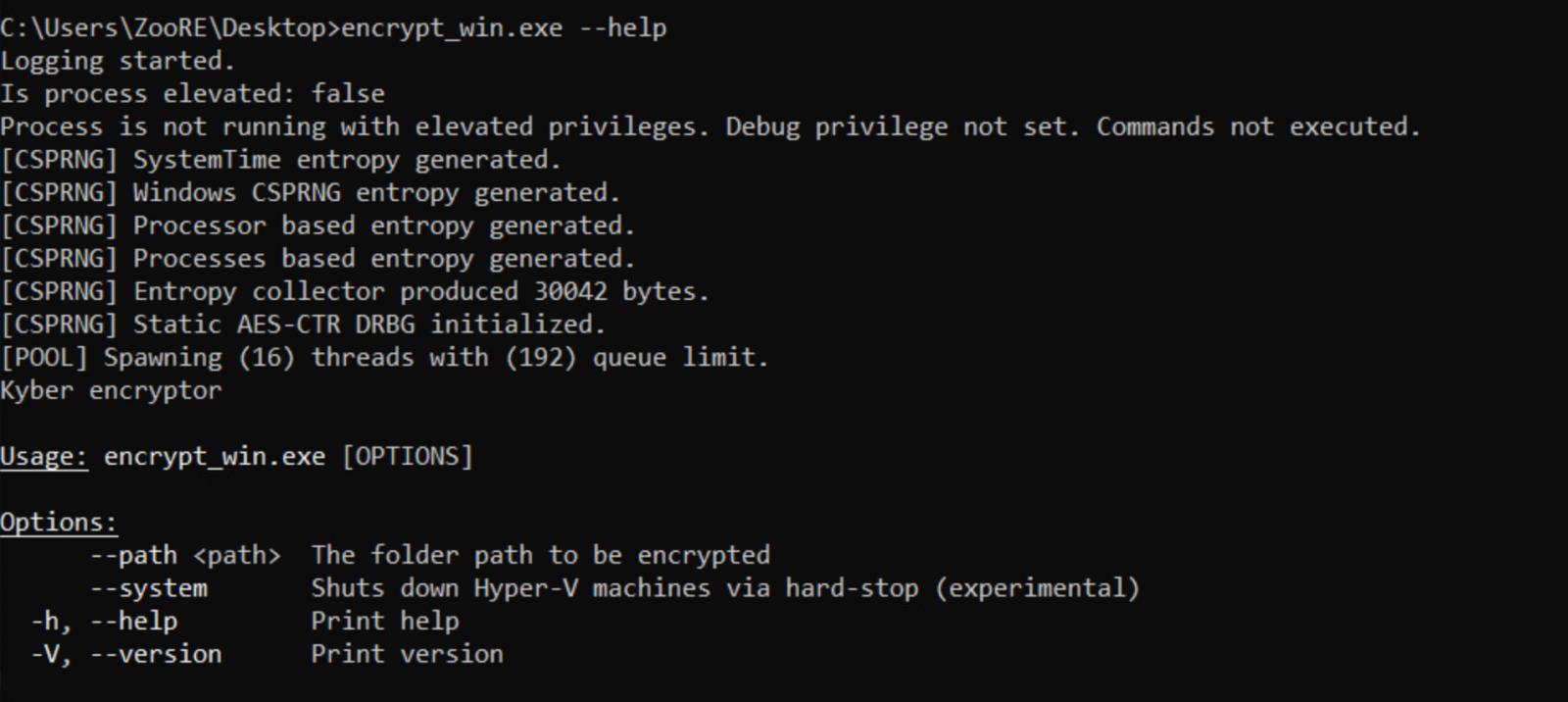
“The Windows variant, written in Rust, includes a self-described “experimental” feature for targeting Hyper-V.”
Coordinated Deployment Across Environments
Additionally, both variants share the same campaign ID and Tor-based ransom infrastructure, indicating that the same ransomware affiliate deployed them. As a result, the attacker likely aimed to maximize impact by encrypting all servers simultaneously.
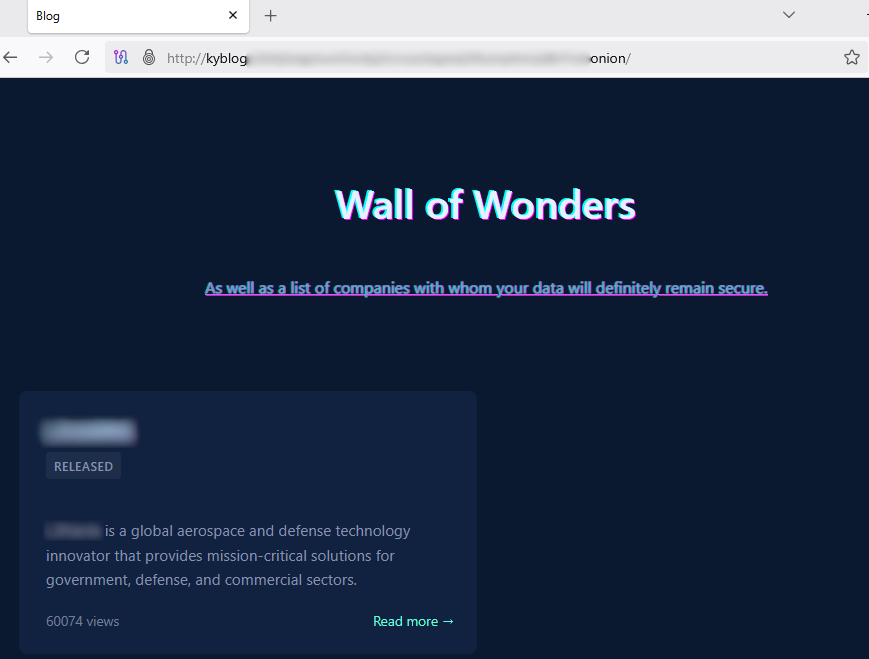
At the time of writing, BleepingComputer has identified only one listed victim on the Kyber data extortion portal—a multi-billion-dollar American defense contractor and IT services provider.
Kyber ransomware victim extortion portal
Source: BleepingComputer.com
Furthermore, Rapid7 reports that the ESXi variant enumerates all virtual machines (VMs) on the infrastructure, encrypts datastore files, and defaces ESXi interfaces with ransom notes that guide victims through payment and recovery.
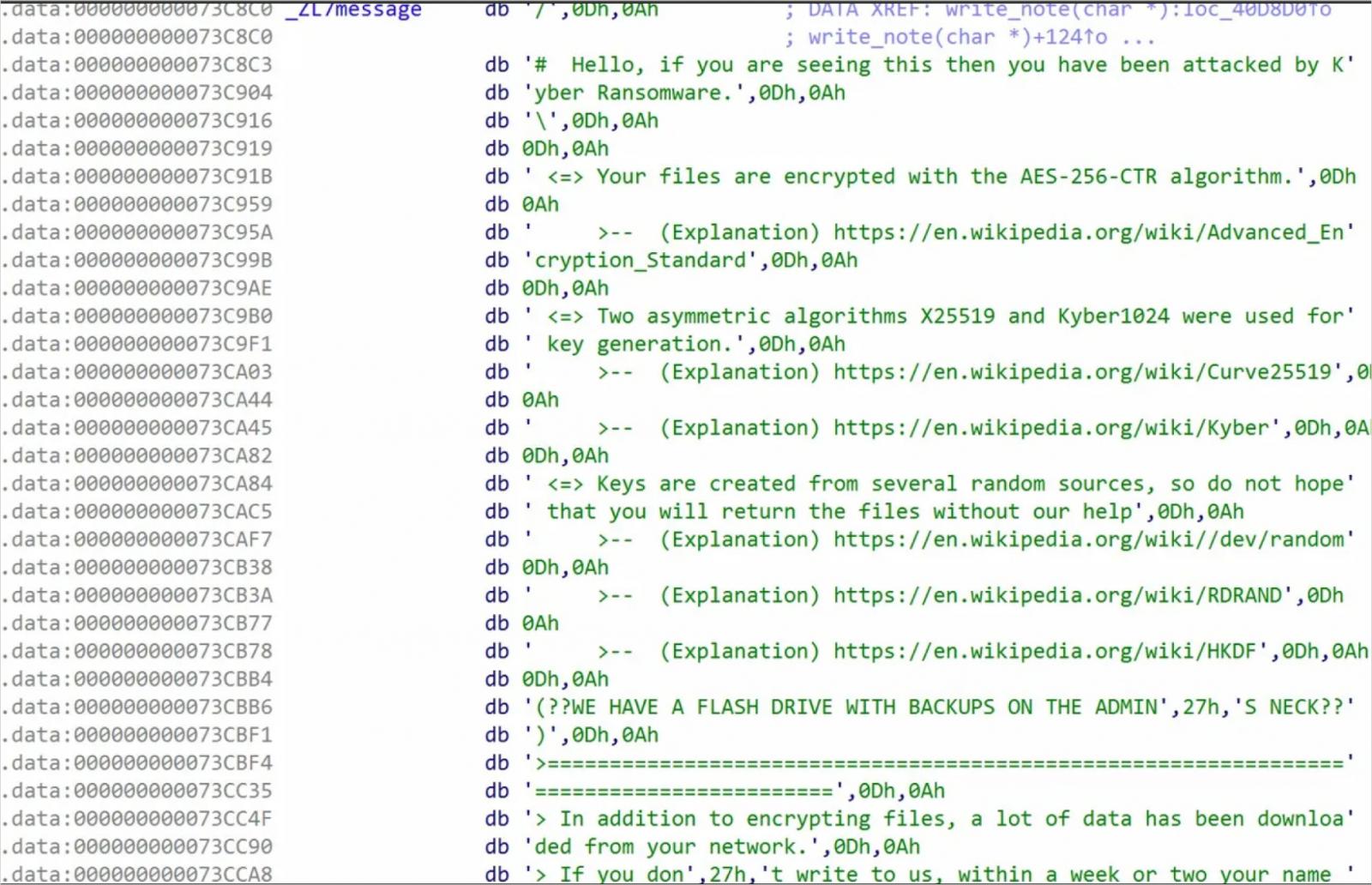
However, although the ransomware advertises ‘post-quantum’ encryption based on Kyber1024 key encapsulation, Rapid7 determined that these claims do not hold true for the Linux ESXi encryptor.
Instead, the Linux version uses ChaCha8 for file encryption and RSA-4096 for key wrapping.
File Encryption Logic
- Small files (<1 MB) are fully encrypted and appended with the ‘.xhsyw’ extension
- Files between 1 MB and 4 MB have only the first MB encrypted
- Files larger than 4 MB are intermittently encrypted based on operator configuration
Ransom note embedded in the ELF binary
Source: Rapid7
In contrast, the Windows variant, written in Rust, implements Kyber1024 and X25519 for key protection, aligning with the claims in the ransom note.
“This confirms that Kyber is not used for direct file encryption. Instead, Kyber1024 protects the symmetric key material, while AES-CTR handles bulk data encryption,” Rapid7 explains.
Importantly, while the use of Post-quantum Cryptography stands out, it does not change the outcome for victims. Whether the Encryptor uses RSA or Kyber1024, files remain unrecoverable without access to the attacker’s private key.
Destructive Capabilities of the Windows Variant
Meanwhile, the Windows variant appends the ‘.#~~~’ extension to Encrypted files, terminates services, deletes backups, and Introduces an experimental feature to shut down Hyper-V virtual machines.
Kyber for Windows CLI
Source: Rapid7
Furthermore, it eliminates multiple recovery paths by:
- Deleting shadow copies
- Disabling boot repair
- Killing SQL, Exchange, and backup services
- Clearing event logs
- Wiping the Windows Recycle Bin
Interestingly, Rapid7 Highlighted an unusual choice of a mutex in the Windows variant, which appears to reference a song on the Boomplay music platform.
Overall, the Windows variant demonstrates greater technical Maturity, while the ESXi variant currently lacks some of its advanced features.
Source: BleepingComputer, Bill Toulas
Read more at Impreza News