Researchers identified a new malware strain called Slopoly, which attackers likely created using generative AI tools. The malware enabled a threat actor to remain on a compromised server for more than a week while stealing data during an Interlock Ransomware attack.
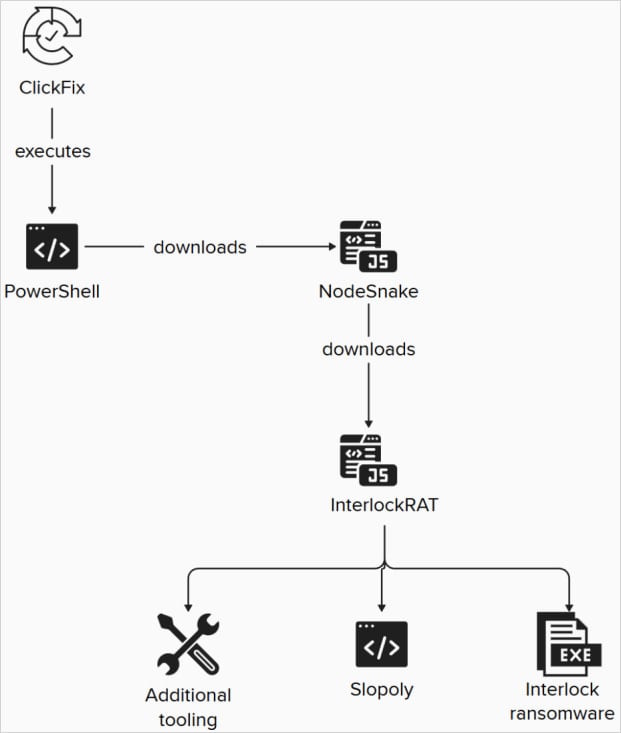
Meanwhile, the breach began with a ClickFix ruse. Later in the attack chain, the hackers deployed the Slopoly backdoor as a PowerShell script that acted as a client for the command-and-control (C2) framework.
Subsequently, IBM X-Force researchers analyzed the script and discovered strong indicators that a large language model (LLM) generated it. However, the researchers could not determine which specific model produced the code.
Notably, several characteristics pointed to AI-assisted malware development. For example, the code contained extensive commentary, structured logging, detailed error handling, and clearly named variables—features rarely seen in human-developed malware.
Furthermore, the researchers attributed the attack to a financially motivated group they track as Hive0163, “whose main objective is extortion through large-scale data exfiltration and ransomware.”
Slopoly Capabilities and Limitations
According to the researchers, Slopoly remains relatively unsophisticated. Nevertheless, its presence in Ransomware operators’ attack chains suggests that criminals actively use AI tools to accelerate custom malware development, which may help them evade detection.
Although comments in the Slopoly script describe it as a “Polymorphic C2 Persistence Client,” IBM X-Force researchers did not identify any capability that allows the malware to modify its own code during execution.
“The script does not possess any advanced techniques and can hardly be considered polymorphic, since it’s unable to modify its own code during execution,” reads the IBM report.
“The builder may, however, generate new clients with different randomized configuration values and function names, which is standard practice among malware builders.”
How the Slopoly Malware Builder Works
Researchers from IBM X-Force believe that a malware builder generated Slopoly and inserted configuration values such as beaconing intervals, command-and-control addresses, mutex names, and session IDs.
Attackers deploy the malware in C:\ProgramData\Microsoft\Windows\Runtime\, where it performs several core functions:
- Collecting system information
- Sending a heartbeat beacon every 30 seconds to /api/commands
- Polling for commands every 50 seconds
- Executing received commands via cmd.exe
- Sending command output back to the C2 server
- Maintaining a rotating persistence.log file
- Establishing persistence through a scheduled task named “Runtime Broker”
Additionally, the supported commands allow the malware to download and execute EXE, DLL, or JavaScript payloads, run shell commands and return results, change beaconing intervals, update itself, or terminate its own process.
Importantly, the attack observed by IBM began with a ClickFix social engineering flow. The attackers also deployed multiple malware components alongside Slopoly, including the NodeSnake and InterlockRAT backdoors.
Attack chain deploying Slopoly in a later stage
Source: IBM X-Force
The Interlock Ransomware operation emerged in 2024 and quickly adopted the ClickFix social engineering technique, later incorporating the FileFix variant.
Previously, the threat group claimed attacks against high-profile organizations such as the Texas Tech University System, DaVita, Kettering Health, and the city of Saint Paul, Minnesota.
Interlock Ransomware Payload and Encryption Behavior
The Interlock Ransomware payload observed in the attacks analyzed by IBM appears as a 64-bit Windows Executable delivered through the JunkFiction loader.
Once executed, the malware can run as a scheduled task with SYSTEM privileges. It also uses the Windows Restart Manager API to release locked files before Encrypting them and appending the ‘.!NT3RLOCK’ or ‘.int3R1Ock’ extensions to the Encrypted copies.
Finally, IBM reports that Hive0163 may share associations with developers behind Broomstick, SocksShell, PortStarter, SystemBC, and operators of the Rhysida Ransomware campaign.
Source: BleepingComputer, Bill Toulas
Read more at Impreza News