Wynn Resorts has confirmed that a hacker stole employee data from its systems after the company appeared on the ShinyHunters extortion gang’s data leak site.
Following the discovery, the company activated its incident response procedures and launched an investigation with assistance from external cybersecurity experts.
“We have learned that an unauthorized third party acquired certain employee data,” reads a statement shared with BleepingComputer.
“Upon discovery, we immediately activated our incident response protocols and launched a thorough investigation with the help of external cybersecurity experts.”
Attackers Claim Data Deletion Amid Ransom Questions
Although Wynn has not stated whether it paid a ransom to prevent the data leak, the company said the attackers confirmed they deleted the stolen data. In past extortion cases, threat actors typically claim deletion only after reaching an agreement with a victim.
“The unauthorized third party has stated that the stolen data has been deleted. We are monitoring and to date have not seen any evidence that the data has been published or otherwise misused,” the statement continued.
Additionally, the company confirmed that the incident did not impact guest operations or its physical properties, which remain fully operational. Wynn also now offers complimentary credit monitoring and identity protection services to affected employees.
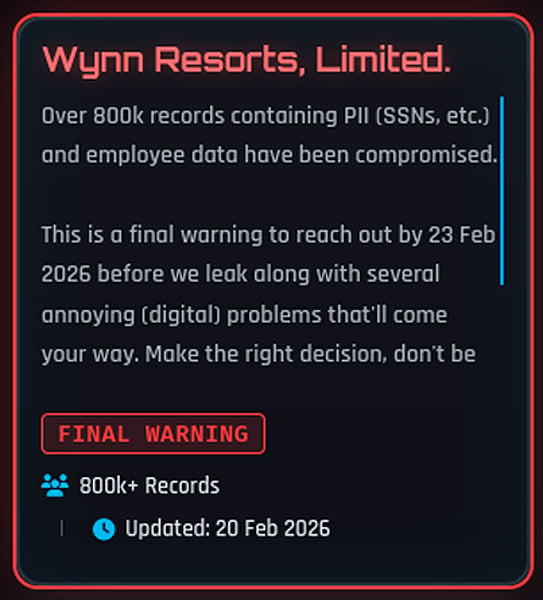
ShinyHunters Threat Post and 800,000 Record Claim
This statement followed Wynn Resorts’ appearance on the ShinyHunters data leak site on Thursday.
In their post, the threat actors claimed they stole:
“PII (SSNs, etc) and employee data”
They also warned the company to make contact before February 23, 2026, or they would publish the data.
“Over 800k records containing PII(SSNs, etc) and employee data have been compromised,” reads the now-deleted post on ShinyHunters data leak site.
“This is a final warning to reach out by 23 Feb 2026 before we leak along with several annoying (digital) problems that’ll come your way. Make the right decision, don’t be the next headling.”
Wynn Resorts listing on the ShinyHunters data leak site
Shortly afterward, the Wynn entry disappeared from the site — a move that often signals ongoing negotiations or disputed claims.
Ransom Payment Unclear as Both Sides Decline Comment
Wynn Resorts did not answer questions about whether it paid a ransom or how many individuals the breach affected. Likewise, ShinyHunters told BleepingComputer they had no comment on whether they received payment.
However, the threat actors previously claimed they stole the data from the company’s Oracle PeopleSoft environment.
ShinyHunters operates as a data extortion group that breaches organizations and threatens to publish stolen data unless victims pay a ransom.
Over the years, the group has claimed responsibility for multiple high-profile data theft incidents and has operated across underground forums and extortion portals.
Last year, ShinyHunters launched a widespread campaign targeting Salesforce environments, using social engineering and stolen third-party OAuth tokens to compromise numerous companies.
More recently, the group has claimed responsibility for additional security breaches involving Panera Bread, Betterment, SoundCloud, Canada Goose, PornHub, and Match Group.
Vishing and Device Code Attacks Target SSO Accounts
In several cases, attackers compromised victims through voice phishing (vishing) attacks that targeted single sign-on (SSO) accounts at Google, Microsoft, and Okta. During these attacks, threat actors posed as IT support staff and tricked employees into entering credentials and multi-factor authentication (MFA) codes into phishing sites.
As BleepingComputer first reported, ShinyHunters recently adopted device code vishing techniques to obtain Microsoft Entra authentication tokens.
After stealing credentials and authentication codes, the attackers hijack victims’ SSO accounts and extract data from connected SaaS applications, including:
- Salesforce
- Microsoft 365
- Google Workspace
- SAP
- Slack
- Adobe
- Atlassian
- Zendesk
- Dropbox
and many others.
Source: BleepingComputer, Lawrence Abrams
Read more at Impreza News