Cybercriminals linked to the government of China (but who operate outside it) have been identified spying on more than 30,000 organizations in the United States, through four zero day vulnerabilities, newly found in the email software for Windows servers, the Microsoft Exchange.
According to independent journalist Brian Krebs, in addition to the more than 30,000 US organizations (which includes small businesses, towns, cities and local governments), companies in Norway and the Czech Republic have also had their emails hacked by a “Chinese cyberespionage unit”, baptized as HAFNIUM, by Microsoft.
The cybercriminal group was identified by the Microsoft Threat Intelligence Center (MSTIC) on Tuesday (3/2). According to the company, based on the analysis of the victims, techniques and procedures used, the group is funded by the Chinese state, but does not operate in China.
“Microsoft has detected multiple zero day exploits being used to attack local versions of Microsoft Exchange Server in limited and targeted attacks. The threat actor used these vulnerabilities to access local Exchange servers, which allowed access to email accounts and allowed additional malware to be installed to facilitate long-term access to victims’ environments“, writes the company.
The Hack contacted Microsoft Brazil, which asks the solution’s customers to contact the company immediately and reports working in partnership with the US Cyber Security and Infrastructure Agency (CISA), in addition to other agencies to offer the best threat mitigation alternative.
“The best method of protection is to apply updates as quickly as possible to all affected systems. We continue to assist our customers by providing additional investigation and mitigation guidance. Impacted customers should contact our support teams for additional help and resources, ”writes a spokesman for Microsoft in Brazil.
Outdated Microsoft Exchange
Microsoft released emergency updates immediately after discovering the vulnerabilities. However, many companies still use older versions of the software (from 2013 to 2019). According to Krebs, the number of companies and users hacked “increased dramatically” after the update was released.
As the journalist explains, a webshell is left behind in the intrusion of each e-mail. This one webshell is responsible for allow cybercriminals, administrator access to the victim’s server: an easy-to-use, password-protected backdoor that can be accessed from any browser.
It is important to remember that there is no point in updating Microsoft Exchange if your server has already been infected with the backdoor. The update only protects servers that have not yet been exploited. To identify if your server is infected, it is necessary to use a Microsoft script, published on Github and, with that, remove all malicious files.
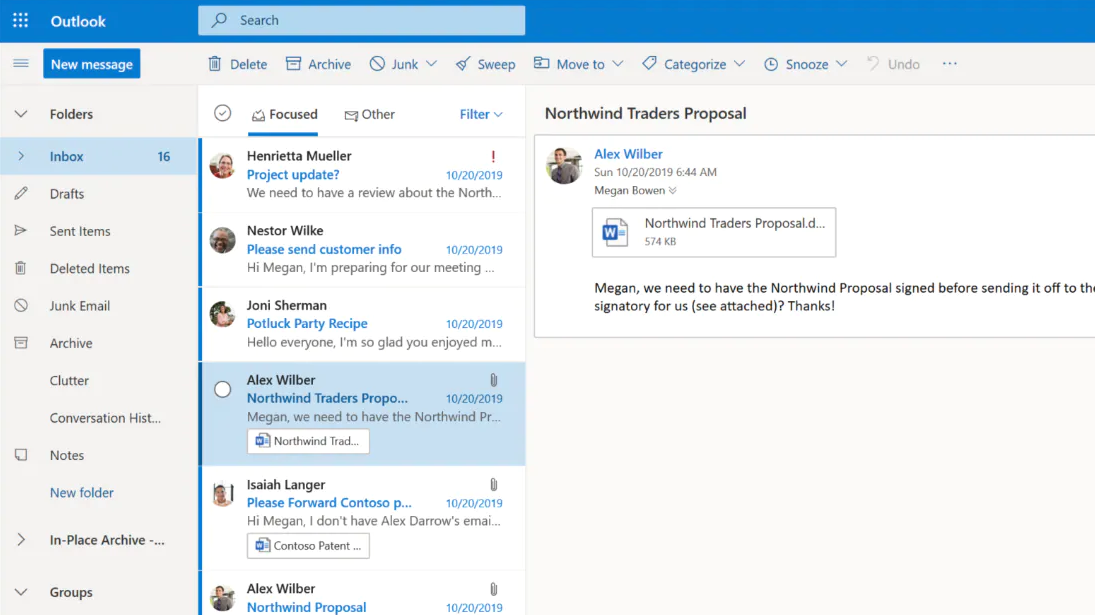
Microsoft Outlook
According to The Register, the zero day vulnerabilities exploited by HAFNIUM are like monsters, the worst nightmares for Microsoft developers, who are likely to deal with vulnerable applications. Vulnerabilities inherited from legacy systems, from traditional code and which are complicated to update.
“This security breach is atrocious. Before patches were released, there was no defense – it was and is a zero day remote pre-authentication code execution vulnerability. Attackers can just roll over, put their webshells and walk away with their data […] If you haven’t lost one night of sleep, you’ll miss two from tomorrow“writes Rupert Goodwins in a column for The Register.
Goodwins explains that Microsoft Outlook users, personal use version of the email service (code very similar to Microsoft Exchange) should also keep their eyes open.
“I don’t know what the source code for Exchange and Outlook looks like: it could be a marvel of engineering, a pleasure to work with and an example of architecture. In this case, however, something went terribly wrong to disguise the fact. Code bases are monsters to test and remedy. The evidence is what we have here“, he explains.
Sources: Microsoft; Github (Microsoft); Krebs on Security; The Register.
See the original post at: https://thehack.com.br/ataque-de-espionagem-massivo-explora-vulnerabilidades-zero-day-em-app-de-e-mail-para-servidores-da-microsoft/?rand=48873