Five vulnerabilities based on code injection on the user side (client side) were discovered by security researcher Pedr4uz, after studying the code of popular pornographic sites, the Pornhub, YouPorn, Redtube and Tube8, for about two months.
According to the researcher, just click on an adulterated link so that an attacker could steal session and user and employee accounts, beyond the records of everything that was done on the site, such as credit card data, if the user made a purchase.
“The only thing that was needed is for the user to click on the link […] If I sent an adulterated link to an employee on one of these sites and he clicked, his session would be mine […] These loopholes could also be used to steal employee accounts, with administrator privileges on the website ”, explains Pedr4uz.
The researcher got $ 1000 as a reward through the bug bounty platform, HackerOne. The reward represents two bugs from Redtube, one from Pornhub and one from YouPorn. Pedr4uz informs that, although Tube8 was also vulnerable, the firewall was configured correctly and the reward was not considered.
“These loopholes were found first on YourPorn, then on all other sites in the same group, everyone was vulnerable, except Tube8, where there was a properly configured firewall. As much as it was possible to control what would be reflected on the user’s page, the firewall blocked my requests ”, he says.
The vulnerability
The researcher says that he has been studying the YouPorn code for some time and during a review process, which he does every week, discovered an HTML page, created to manage ads that will be displayed to the user.
“A blank HTML page, which takes some user variables, defines which ad server will be and places this ad on that page, which, in theory, the user should not access or even know that exists”, he explains.
With this curious discovery, the researcher decided to investigate, with tests of different parameters. “I discovered a few different parameters, that when I put it in the URL, in an encoded way, the ads page decoded them“, it says.
He identified that the page also decoded some special characters. That was when he discovered the vulnerability: it was possible to take advantage of this character decoding to attach malicious code to the page’s source code.
“If that HTML page was running a simple script, which only selects ads on the server, it was possible to insert arbitrary JavaScript and HMTL and thereby steal the user’s cookies and session. It was also possible to make the victim’s browser download malicious software without authorization and much more ”, he explains.
Pedr4uz knew that the YouPorn code was very similar to the code on other sites of the same company (Pornhub, Redtube and Tube8 and others) and decided to test them too. The same bug was found on all other sites, as they were developed with very similar technology.
“The topology of Pornhub, Redtube, to YouPorn and Tube8 are almost analogous, almost 90% identical […] Realized that a lot of YouPorn also applied to Pornhub, Redtube and Tube8. I found this strange and saw that the company that manages the YouPorn bounty bug is the same as the others. Then it all made sense. I started exploring the topology of all other sites in the same company. But my main focus has always been Youporn ”, he says.
The process
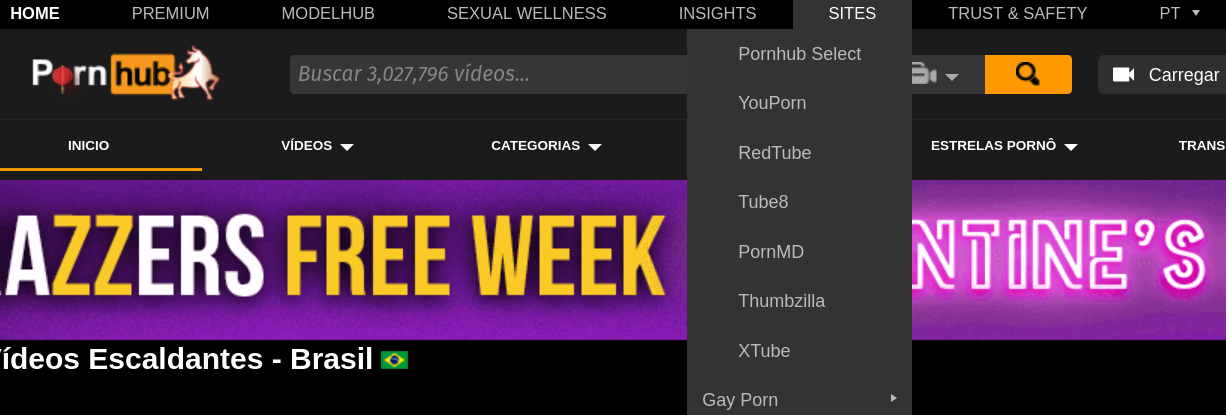
MindGeek, the company responsible for the websites in question, is the true conglomerate of digital whoring. In addition to Pornhub, YouPorn, Redtube and Tube8 the company, with offices in Canada, the United States, the United Kingdom, Ireland, Germany, Romania and Italy, also manages the sites PornMD, Thumbzilla and Xtube, in addition to adult film producers Brazzers, Digital Playgroud, Men, WhyNotBi, Reality Kings and Sean Cody.
According to the company itself, only Pornhub, one of its main products, receives an average of over 100 billion video views per year and has about 20 million registered users.
Pedr4uz says that during these two months studying YouPorn, several vulnerability reports were sent – some very serious that allowed more serious attacks like “Cache Poisoning” and “DNS Spoofing”, directed at the company’s server – but all were considered duplicates , which is when the bug has already been reported and the company is still in the process of fixing it.
Until on any given Sunday, during the weekly review, he identified this suspicious page, discovered the problem, reported it to the company and received the reward. For the researcher, bug bounty is a matter of time and dedication.
“There were several other loopholes that I have not yet managed to scale as a valid vulnerability, but being able to put together a scenario of appropriate loopholes is a matter of time”, He concludes.
Soure: The Hack