A new report shows that hackers are selling access to 576 corporate networks worldwide for a total cumulative sales price of $4,000,000, fueling attacks on the enterprise.
The research comes from Israeli cyber-intelligence firm KELA which published its Q3 2022 ransomware report, reflecting stable activity in the sector of initial access sales but a steep rise in the value of the offerings.
Although the number of sales for network access remained about the same as in the previous two quarters, the cumulative requested price has now reached $4,000,000.
For comparison, the total value of initial access listings in Q2 2022 was $660,000, recording a drop in value that coincided with the summer ransomware hiatus that hurt demand.
The road to ransomware
Initial access brokers (IABs) are hackers who sell access to corporate networks, usually achieved through credential theft, webshells, or exploiting vulnerabilities in publicly exposed hardware.
After establishing a foothold on the network, the threat actors sell this corporate access to other hackers who use it to steal valuable data, deploy ransomware, or conduct other malicious activity.
The reasons IABs choose not to leverage network access vary, ranging from lacking diverse intrusion skills to preferring not to risk increased legal trouble.
IABs still play a crucial role in the ransomware infection chain, even if they got sidelined last year when big ransomware gangs that operated as crime syndicates operated their own IAB departments.
Q3 ’22 numbers
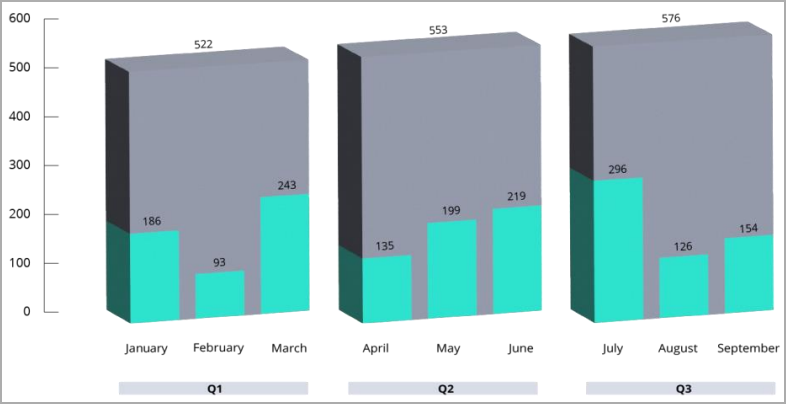
In the third quarter of 2022, KELA’s analysts observed 110 threat actors posting 576 initial access offerings totaling a cumulative value of $4,000,000.
Monthly volume of initial access sales (KELA)
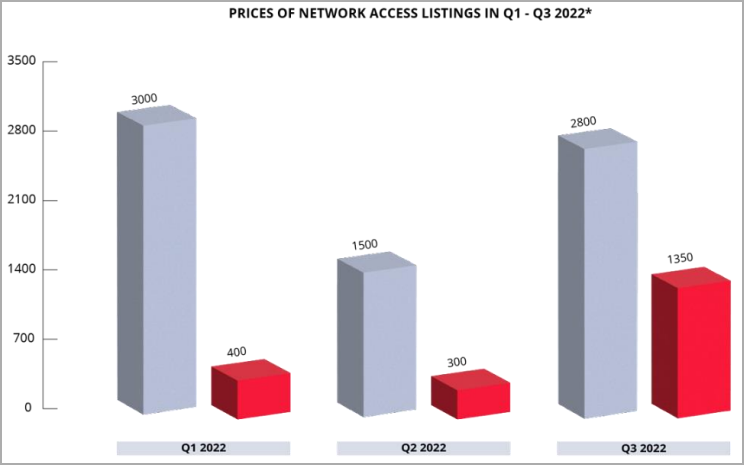
The average selling price of these listings was $2,800, while the median selling price reached a record figure of $1,350.
Initial access sales prices (KELA)
KELA also saw a case of a single access being offered for purchase at the astronomical price of $3,000,000. However, this listing was not included in the Q3 ’22 stats and totals due to doubts about its authenticity.
The top three IABs operated a large-scale business, offering between 40 and 100 accesses for sale in Q3 2022.
Based on hacking forum discussions and marketplace listing removal events, the average time to sell corporate access was just 1.6 days, while most were of RDP and VPN types.
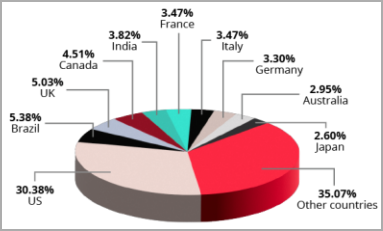
This quarter’s most targeted country was the United States, accounting for 30.4% of all IAB offerings. This stat is close to the 39.1% share of ransomware attacks in Q3 targeting U.S. companies.
Most targeted countries by IABs in Q3 (KELA)
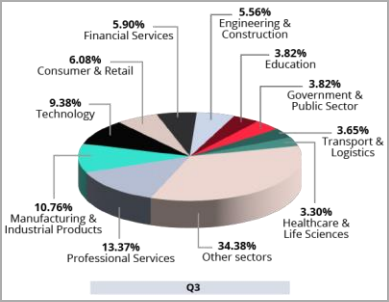
When looking at the targeted sectors, professional services, manufacturing, and technology topped the list with 13.4%, 10.8%, and 9.4%, respectively. Again, ransomware attacks feature a similar ranking, emphasizing the connection between the two.
Sectors IABs targeted the most in Q3 (KELA)
As initial access brokers have become an integral part of the ransomware attack chain, properly securing your network from intrusion is crucial.
This includes placing remote access servers behind VPNs, restricting access to publicly exposed devices, enabling MFA, and conducting phishing training to prevent the theft of corporate credentials.
Source: BleepingComputer, Bill Toulas