They warn that WordPress Advanced Custom Fields and Advanced Custom Fields Pro plugins with millions of installs are flawed and vulnerable to cross-site scripting (XSS) attacks.
Buggy WordPress plugins that allow XSS attacks on websites
Both plugins are among the most popular WordPress custom field builders with 2,000,000 active installs on websites worldwide. Patchstack researcher Rafie Muhammad discovered the high severity reflected XSS vulnerability on May 2, 2023, which was assigned the identifier CVE-2023-30777.
XSS bugs often allow attackers to inject malicious script into websites viewed by others, resulting in code execution in the visitor’s web browser. Patchstack says the XSS flaw could allow an unauthenticated attacker to steal sensitive information and increase their privileges on an affected WordPress site.
Note that this vulnerability can be triggered on a default installation or configuration of the Advanced Custom Fields plug-in. XSS can also only be triggered by logged in users who have access to the Advanced Custom Fields plugin.
Patchstack
This means that the unauthenticated attacker would still have to socially engineer someone with access to the plugin to visit a malicious URL to trigger the flaw. The plugin developer was notified of the issue after Patchstack was discovered and released a security update on May 4, 2023, version 6.1.6.
The XSS flaw
The XSS flaw The CVE-2023-30777 flaw stems from the ‘admin_body_class’ function handler failing to properly clean up the output value of a hook that controls and filters CSS classes (design and layout) for the main body tag in the admin area of WordPress sites.
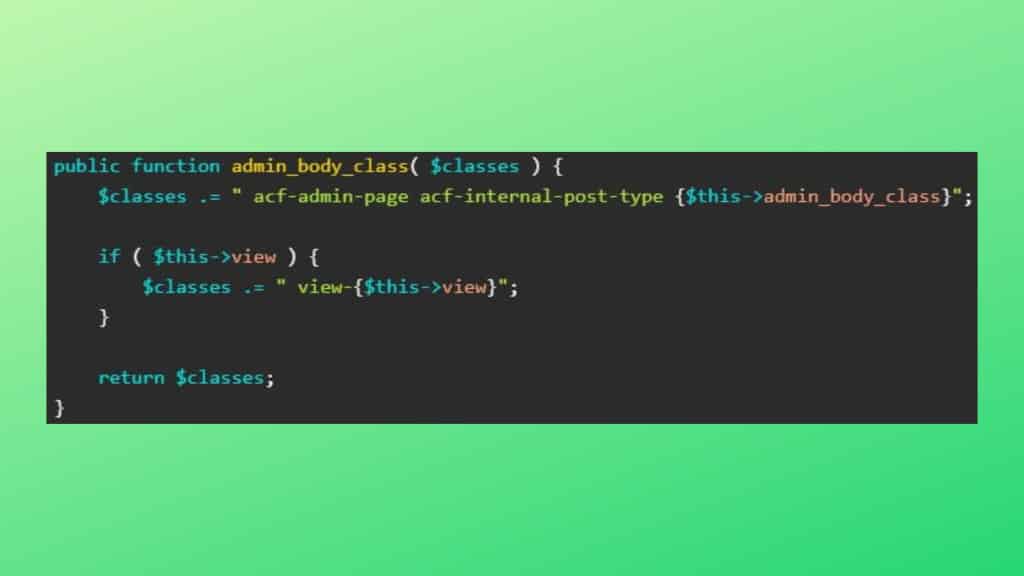
An attacker could take advantage of unsafe direct code concatenation in the plugin code, specifically the ‘$this?view’ variable, to add harmful code (XSS DOM payloads) into your components that will pass into the final product, a class string .
The cleanup function used by the plugin, ‘sanitize_text_field’, will not stop the attack because it will not detect the malicious code injection. The developer fixed the bug in version 6.1.6 by implementing a new function called ‘esc_attr’ which properly sanitizes the output value of the admin_body_class hook, therefore preventing XSS.
All Advanced Custom Fields and Advanced Custom Fields Pro users are advised to upgrade to version 6.1.6 or later as soon as possible. While WordPress offers many standard security tools such as secure login, strong passwords and security plugins, it is important to remember that no platform is 100% secure. To keep your website secure, it is necessary to have a regular backup plan and constant updates for WordPress, theme and plugins.
To prevent your website from attacks, losses, not be one of those affected by plugin failure and use WordPress safely. choose a SECURE backup service for your website:
source: Ciso Advisor