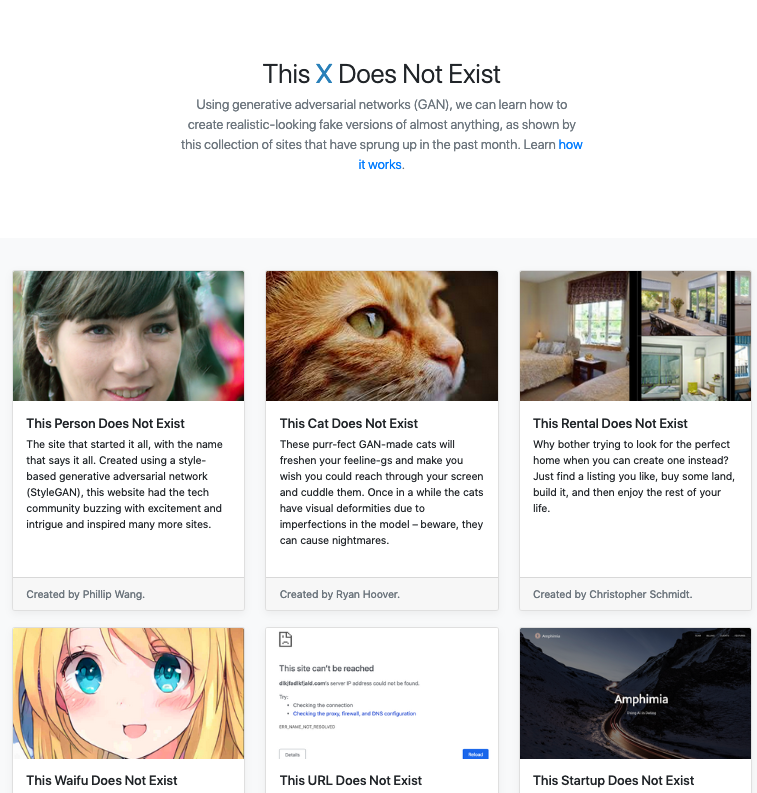
Trend Micro today published a survey showing several scenarios in which drivers can encounter attacks that threaten their safety in connected cars. The survey, called “Cyber Security for Connected Cars: Exploring Risks in 5G, Cloud and Other Connected Technologies”, assessed 29 real attack scenarios in the DREAD 1 threat model in qualitative risk analysis. These are attacks that can be launched against or from the vehicle:
- DDoS attacks on Intelligent Transport Systems (ITS) can overwhelm connected car communications and pose risk
- Exposed and vulnerable connected car systems are easily discovered, increasing the risk of abuse
- More than 17% of all attack vectors examined were at high risk – they require limited knowledge of connected car technology and can be used by low-skill attackers
More than 125 million passenger cars with built-in connectivity are expected to hit the market worldwide between 2018 and 2022, and progress continues to move towards fully autonomous vehicles. This advance will create a complex ecosystem comprising cloud, IoT, 5G and other important technologies. It also has a huge attack surface that potentially comprises millions of endpoints and end users, the company says. The global automotive cybersecurity market is expected to reach $ 5.56 billion by 2025, according to research by the company Million Insights.
To mitigate the risks described in the study, the security of the connected car must be designed, according to Trend Micro, with an integrated view of all critical areas to protect the end-to-end data supply chain.
Trend Micro puts the following high-level guidance on protecting connected cars:
- Make a commitment and have effective alert, containment and mitigation processes
- Protect the end-to-end data supply chain across your car’s E / E network, network infrastructure, back-end servers and Vehicle Security Operations Center (VSOC)
- Apply lessons learned to further strengthen defenses and prevent recurrence of incidents
- Relevant security technologies include firewall, encryption, device control, application security, vulnerability scanner, code signing, IDS for CAN, AV for main unit and more
With international agencies
See the original post at: https://www.cisoadvisor.com.br/29-cenarios-ja-ameacam-a-seguranca-dos-carros-conectados/?rand=59039