Security researcher Alex Birsan discovered a very simple and curious new way to carry out a supply chain attack – and, even more serious, he managed to reach big names in the technology market with his proof of concept. Microsoft, Apple, Uber, Netflix, PayPal, Shopify and Tesla are just a few names that have been affected by the “harmless attack”; in total 35 companies were susceptible.
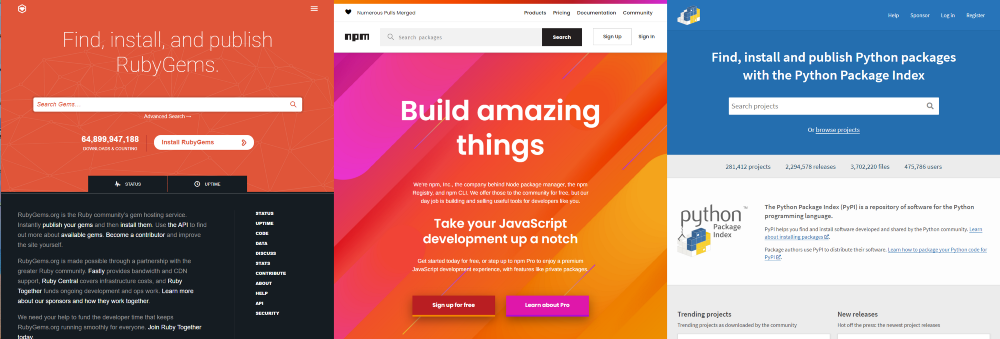
Unlike what happened recently with SolarWinds, Birsan did not have to use offensive techniques or hack into any IT platform maintained by multinational suppliers. All he did was take advantage of the fact that many applications and online services use modified versions of open source projects, including repositories like PyPI, npm and RubyGems.
The idea came up when the expert got access to a JSON manifest that showed that PayPal used a custom npm package called “analytics-paypal” internally. Birson wondered what would happen if the company’s systems found another repository with the same name and with a more recent update date on GitHub, and created a fake edition of the package with an adulterated script.
Bingo! The system ignores the customized package stored on a closed server and depends on the one hosted publicly on GitHub, possibly contracting malware. All of the “clones” created by Birson had a message saying that the content was only “for security research purposes”, but that did not prevent companies from accidentally using it.
I got confused
To the attack, the researcher called it “dependency confusion” and managed to prove that, with this, he would be able to filter sensitive data from the affected servers. “The confusion of addiction is very different from typosquatting or brandjacking, as it does not require any type of manual entry by the victim”, he explains.
“Vulnerabilities or design flaws in automated construction or installation tools can cause public facilities are confused with internal facilities with exactly the same name”, He concludes.
Birson’s discoveries earned him a total of $130,000 in rewards of bounty bug. Both Microsoft and Yelp have issued announcements saying they have reconfigured their package managers to avoid further confusion in the future; Apple and PayPal, contacted by Bleeping Computer, confirmed the reward offered, but offered no further details about the incident.
Source: Bleeping Computer
See the original post at: https://thehack.com.br/pesquisador-invade-microsoft-apple-paypal-e-netflix-usando-so-codigo-aberto/?rand=48873