After the discovery of four zero-day vulnerabilities in Microsoft Exchange, earlier this month, the number of attempted attacks on companies using the tool increased by 1028%, going from 700 in the first week, to 7,200 in the second week of March, informs the research team at Check Point, an Israeli information security provider.
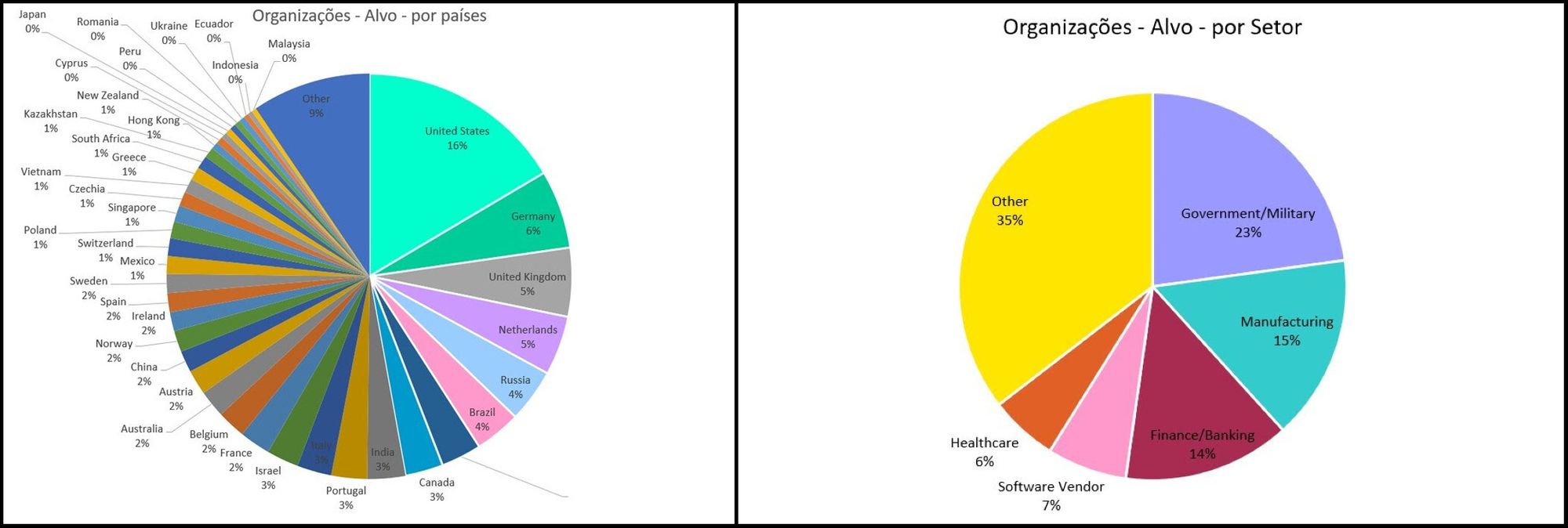
According to the researchers, in this scenario, Brazil and Russia share the fourth most attacked countries, with 4% each, lagging behind the United States (17%), Germany (6%) and the United Kingdom (5%). Government agencies, government suppliers and armies are among the most affected, with 23%. The second place goes to the manufacturing industry, with 15%; banks and financial institutions account for 14%; software providers, 7% and health sector with 6%.
These vulnerabilities allow cybercriminals to access user email accounts from a Windows server, equipped with Microsoft Exchange software, an email service very similar to Microsoft Outlook. If climbing, the vulnerabilities can be used to take complete control of an outdated server.
“Once a cybercriminal takes control of the Exchange server, he can open the network to the internet and access it remotely. Since many Exchange servers are connected to the internet and integrated into the general network, this poses a critical security risk for millions of companies“writes Check Point in a press release.
Threat to national industry
The Hack contacted the country manager, Carlos Rodrigues, from Varonis, who is investigating the situation with its customers, to understand the level of threat that these vulnerabilities pose to Brazilian industry.
For the executive, Brazil is a global target for cybercriminals and the number of attacks directed at national companies is growing. In addition, Microsoft Exchange vulnerabilities can pose an even more worrying threat to the Brazilian economy, since here, most companies operate with internal servers.
“The number of attacks in Brazil has increased a lot recently. In reality, the country is a global target for hackers. In Brazil, most companies still operate on-premises Exchange servers [internos]. There are groups working strongly in the country, so organizations need to operate in order to prevent incidents, ”he says.
Carlos explains that, especially in this last week of March, several different groups took advantage of the newly discovered vulnerabilities to spy and steal data from companies simultaneously. What hinders the investigative work of the police and security researchers.
“Several groups attacked simultaneously, with the objective of maximizing the result of the attacks, generating an enormous effort for the victims. Probably, at this very moment, other groups and criminals are also gaining access to information, multiplying and polarizing the form of attack.. This makes tracking and applying solutions an increasingly complex process, ”explains Carlos.
Update is not automatic and must be done manually
The four zero-day vulnerabilities were fixed in an update released on March 2, after Microsoft identified cybercriminals linked to the Chinese government spying on over 30 thousand North American organizations.
It is important to remember that, by default, updates are not automatic and must be done manually, through Microsoft Exchange itself, or through the “Microsoft Exchange On-Premises Mitigation Tool”, an interactive tool, developed to help companies that do not have an internal technology team to update their systems.
“The problem is that, almost always, there is a“ delay ”between the launch of the patch and the update by the user. That’s why, it is essential that the operating system is configured to receive automatic updates”, Concludes the executive.
See the original post at: https://thehack.com.br/ataques-contra-servidores-microsoft-exchange-crescem-1028-em-uma-semana/?rand=48873